Aes 256 Key Generator C#
 -->
-->Definition
13 days ago I am trying to do decryption in Node.js and encryption in C# with AES CBC 256. I have 16 byte key. I need 32 byte for AES CBC 256 method in Node.js. I tried using Buffer.alloc(32,16-byte-key). Dim plaintext As String = Nothing ' Create an Aes object ' with the specified key and IV. Using aesAlg As Aes = Aes.Create aesAlg.Key = Key aesAlg.IV = IV ' Create a decryptor to perform the stream transform. Convert Aes.Key to SecureString in C#. Ask Question Asked 5 years, 6 months ago. Active 5 years, 6 months ago. Viewed 2k times 0. How do I convert Aes.Key to a secureString? I am doing a byte - string - securestring. I am facing a different problem. Random number generator only generating one random number. How to convert.
Your key needs to be 32 bytes while your IV needs to be 16 bytes (based on your 256 bit key and 128 bit block). If you look at my code, you will see how I handle this using the PadLeft method. How to do AES key generation in C#? AES encrypted message and plain text lenght difference. AES was designed to be efficient in both hardware and software, and supports a block length of 128 bits and key lengths of 128, 192, and 256 bits. How secure is AES encryption algorithm? AES encryption is used by U.S. For securing sensitive but unclassified material, so we can say it is enough secure. Encryption Key Generator. The all-in-one ultimate online toolbox that generates all kind of keys! 64-bit 128-bit 256-bit. Select all Select next Get new results Try our beta version. Security level. 64-bit 128-bit 256-bit 512-bit 1024-bit 2048-bit 4096-bit.
Represents the abstract base class from which all implementations of the Advanced Encryption Standard (AES) must inherit.
- Derived
Examples
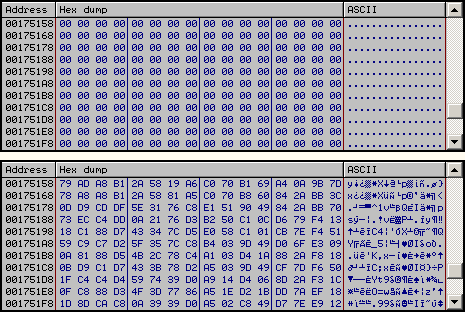
The following example demonstrates how to encrypt and decrypt sample data by using the Aes class.
Constructors
| Aes() | Initializes a new instance of the Aes class. |
Fields
| BlockSizeValue | Represents the block size, in bits, of the cryptographic operation. (Inherited from SymmetricAlgorithm) |
| FeedbackSizeValue | Represents the feedback size, in bits, of the cryptographic operation. (Inherited from SymmetricAlgorithm) |
| IVValue | Represents the initialization vector (IV) for the symmetric algorithm. (Inherited from SymmetricAlgorithm) |
| KeySizeValue | Represents the size, in bits, of the secret key used by the symmetric algorithm. (Inherited from SymmetricAlgorithm) |
| KeyValue | Represents the secret key for the symmetric algorithm. (Inherited from SymmetricAlgorithm) |
| LegalBlockSizesValue | Specifies the block sizes, in bits, that are supported by the symmetric algorithm. (Inherited from SymmetricAlgorithm) |
| LegalKeySizesValue | Specifies the key sizes, in bits, that are supported by the symmetric algorithm. (Inherited from SymmetricAlgorithm) |
| ModeValue | Represents the cipher mode used in the symmetric algorithm. (Inherited from SymmetricAlgorithm) |
| PaddingValue | Represents the padding mode used in the symmetric algorithm. (Inherited from SymmetricAlgorithm) |
Properties

Product Key Generator
| BlockSize | Gets or sets the block size, in bits, of the cryptographic operation. (Inherited from SymmetricAlgorithm) |
| FeedbackSize | Gets or sets the feedback size, in bits, of the cryptographic operation for the Cipher Feedback (CFB) and Output Feedback (OFB) cipher modes. (Inherited from SymmetricAlgorithm) |
| IV | Gets or sets the initialization vector (IV) for the symmetric algorithm. (Inherited from SymmetricAlgorithm) |
| Key | Gets or sets the secret key for the symmetric algorithm. (Inherited from SymmetricAlgorithm) |
| KeySize | Gets or sets the size, in bits, of the secret key used by the symmetric algorithm. (Inherited from SymmetricAlgorithm) |
| LegalBlockSizes | Gets the block sizes, in bits, that are supported by the symmetric algorithm. |
| LegalKeySizes | Gets the key sizes, in bits, that are supported by the symmetric algorithm. |
| Mode | Gets or sets the mode for operation of the symmetric algorithm. (Inherited from SymmetricAlgorithm) |
| Padding | Gets or sets the padding mode used in the symmetric algorithm. (Inherited from SymmetricAlgorithm) |
Methods
| Clear() | Releases all resources used by the SymmetricAlgorithm class. (Inherited from SymmetricAlgorithm) |
| Create() | Creates a cryptographic object that is used to perform the symmetric algorithm. |
| Create(String) | Creates a cryptographic object that specifies the implementation of AES to use to perform the symmetric algorithm. |
| CreateDecryptor() | Creates a symmetric decryptor object with the current Key property and initialization vector (IV). (Inherited from SymmetricAlgorithm) |
| CreateDecryptor(Byte[], Byte[]) | When overridden in a derived class, creates a symmetric decryptor object with the specified Key property and initialization vector (IV). (Inherited from SymmetricAlgorithm) |
| CreateEncryptor() | Creates a symmetric encryptor object with the current Key property and initialization vector (IV). (Inherited from SymmetricAlgorithm) |
| CreateEncryptor(Byte[], Byte[]) | When overridden in a derived class, creates a symmetric encryptor object with the specified Key property and initialization vector (IV). Pc auto shutdown key generator. (Inherited from SymmetricAlgorithm) |
| Dispose() | Releases all resources used by the current instance of the SymmetricAlgorithm class. (Inherited from SymmetricAlgorithm) |
| Dispose(Boolean) | Releases the unmanaged resources used by the SymmetricAlgorithm and optionally releases the managed resources. (Inherited from SymmetricAlgorithm) |
| Equals(Object) | Determines whether the specified object is equal to the current object. (Inherited from Object) |
| GenerateIV() | When overridden in a derived class, generates a random initialization vector (IV) to use for the algorithm. (Inherited from SymmetricAlgorithm) |
| GenerateKey() | When overridden in a derived class, generates a random key (Key) to use for the algorithm. (Inherited from SymmetricAlgorithm) |
| GetHashCode() | Serves as the default hash function. (Inherited from Object) |
| GetType() | Gets the Type of the current instance. (Inherited from Object) |
| MemberwiseClone() | Creates a shallow copy of the current Object. (Inherited from Object) |
| ToString() | Returns a string that represents the current object. (Inherited from Object) |
| ValidKeySize(Int32) | Determines whether the specified key size is valid for the current algorithm. (Inherited from SymmetricAlgorithm) |
Explicit Interface Implementations
| IDisposable.Dispose() | Releases the unmanaged resources used by the SymmetricAlgorithm and optionally releases the managed resources. (Inherited from SymmetricAlgorithm) |
Applies to
Chilkat • HOME • Android™ • Classic ASP • C • C++ • C# • Mono C# • .NET Core C# • C# UWP/WinRT • DataFlex • Delphi ActiveX • Delphi DLL • Visual FoxPro • Java • Lianja • MFC • Objective-C • Perl • PHP ActiveX • PHP Extension • PowerBuilder • PowerShell • PureBasic • CkPython • Chilkat2-Python • Ruby • SQL Server • Swift 2 • Swift 3/4 • Tcl • Unicode C • Unicode C++ • Visual Basic 6.0 • VB.NET • VB.NET UWP/WinRT • VBScript • Xojo Plugin • Node.js • Excel • Go
Aes 256 Encryption Key Generator C#
| Demonstrates how to use RSA to protect a key for AES encryption. It can be used in this scenario: You will provide your RSA public key to any number of counterparts. Your counterpart will generate an AES key, encrypt data (or a file) using it, then encrypt the AES key using your RSA public key. Your counterpart sends you both the encrypted data and the encrypted key. Since you are the only one with access to the RSA private key, only you can decrypt the AES key. You decrypt the key, then decrypt the data using the AES key. This example will show the entire process. (1) Generate an RSA key and save both private and public parts to PEM files. (2) Encrypt a file using a randomly generated AES encryption key. (3) RSA encrypt the AES key. (4) RSA decrypt the AES key. (5) Use it to AES decrypt the file or data.
| |||||
© 2000-2020 Chilkat Software, Inc. All Rights Reserved.